Congratulations to team of Department of Computer Science (CS) faculty and doctoral students that earned as a Best Paper Award at the 2021 Applied Research Competition by Cybersecurity Games & Conference (CSAW ’21).
Brian Kondracki presented, Catching Transparent Phish: Analyzing and Detecting MITM Phishing Toolkits, which secured third place. In addition to Kondracki, collaborators include Babak Amin Azad, Oleksii (Alex) Starov (Palo Alto Networks) and Professor Nick Nikiforakis. Overall, the conference has 1,600 qualified teams out of 6,000 annual competitors.
According to CSAW, “This "Best Paper Award" assesses the top scholarly security research from the previous year. The focus of this competition is on research that has a practical impact. With eligibility limited to already published papers or camera-ready papers, CSAW has a reputation for drawing some of the best security research worldwide.”
The team’s research focuses on analyzing Man-in-the-Middle (MITM) phishing toolkits where toolkits act as malicious reverse proxy servers of online services, mirroring live content to users while extracting credentials and session cookies. By analyzing and experimenting with these toolkits, the SBU team finds intrinsic network-level properties that can be used to identify such toolkits and develops a machine learning classifier that identifies its presence in online communications with 99.9% accuracy.
“The recognition from CSAW acknowledges the team’s relentless work to stop phishing attempts as they occur,” said Professor Nick Nikiforakis.
The paper discusses the discovery of MITM phishing toolkits which occupy a blind spot in phishing blocklists. Only 43.7% of domains and 18.9% of IP addresses associated with MITM phishing toolkits are present on blocklists, leaving unsuspecting users vulnerable to these attacks. Results show that the detection scheme is resilient to the cloaking mechanisms incorporated by these tools and can detect previously hidden phishing content. Finally, the paper details proposed methods that online services can utilize to fingerprint requests originating from these toolkits.
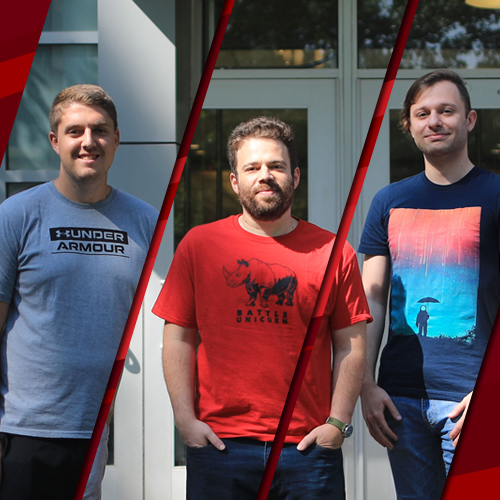
About the Researchers
Nick Nikiforakis is an associate professor in the Department of Computer Science. His research interests include web security and privacy, software security, DNS, intrusion detection, and cybercrime. He is actively involved in topics such as the measurement and reduction of attack surface in web applications, understanding DNS abuse, and identification of security and privacy issues specific to mobile web browsers. Nikiforakis leads the efforts of the PragSec Lab at Stony Brook University.
Oleksii (Alex) Starov is a security researcher, scientist and philosopher. His research focuses on proactive and data-driven web security, online privacy, cybercrime. Currently, he manages the innovative web security research team at Palo Alto Networks, on protecting web users against sophisticated cyberattacks. He received his PhD in Computer Science from Stony Brook University where he was advised by Nikiforakis.
Brian Kondracki, a Ph.D. candidate based out of the PragSec Lab at Stony Brook University, earned his B.S. and M.S. in computer science, with specialization in computer security from Stony Brook University. He is working on developing techniques to identify networked entities using characteristics of their behavior. His research focuses on web and network security.
PhD student Babak Amin Azad conducts research in the PragSec Lab and his area of research spans web and mobile security topics. The study of Android malware and scam economy (Telescam.ir project) and analysis of internet bots and automated attacks are among these topics.
About CSAW
CSAW [see-SAW] is the most comprehensive student-run cyber security event in the world, featuring eight cyber competitions, workshops, and industry events. Final events are hosted by five global academic centers. Recordings from CSAW’21 can be found on the NYU Tandon YouTube CSAW'21 Playlist.
Learn more about the related research by visiting: https://catching-transparent-phish.github.io/
